Report 01 - Real-world Hardware Security Incident
2026-02-08 | Report , Real-world Incidents
Introduction
Hardware security is a critical aspect of safeguarding the technological infrastructure we rely on daily. Understanding real-world incidents provides invaluable insights into the consequences of security flaws and the measures needed to prevent them. In this assignment, you will analyze a real-world hardware security incident from the last four years, focusing on its cause, impact, and aftermath.
Instructions
- Identify and research a real-world hardware security incident. Search from the linked resources below or similar. Claim your incident on the forum.
- Produce a summary slide similar to those presented in the Week 1 lab. Analyze and explain the cause and consequences of this hardware security incident.
- Produce an extended abstract as a short document which presents the incident in more detail and links to supplementary sources.
Deliverables
-
Max Two-Page two-column IEEE-conference-formatted extended abstract (2.5%)
- Covers a single hardware security incident from the last four years.
- Includes cause, consequences, and aftermath of the incident.
- At least one picture or diagram is required.
- Adheres to two-column IEEE conference format guidelines.
- Word template: https://www.ieee.org/content/dam/ieee-org/ieee/web/org/conferences/conference-template-a4.docx
- Overleaf template: https://www.overleaf.com/gallery/tagged/ieee-official
- (use the IEEE conference template)
- Aim to cite around 5-6 references.
-
Summary Slide in PowerPoint format (1%)
- Summarizes the report’s key points.
- Designed for clarity and visual appeal.
- Single slide only!
- Presenter notes can be included.
Note: No two students can present the same real-world incident. You must “stake a claim” to your incident in the class forum.
Resources
Students may find the following sources helpful when looking for hardware security incidents.
- Google Scholar (search hardware security)
- Papers published in IEEE S&P, USENIX SEC, IEEE TIFS, IEEE TDSC, and others
- Reporting by Wired, New Scientist, and other tech magazines
- Technical blogs by Krebs on Security and others
- presentations at DEFCON, BlackHat, and CCC
- etc.
Grading Rubric
Extended Abstract (2.5%)
- Criterion:
- (1%) Content Coverage:
- Poor (0.25%): Barely covers the incident, missing key details about cause and consequences.
- Fair (0.5%): Covers the incident but lacks depth in analysis of cause and consequences.
- Good (0.75%): Provides a clear overview of the incident, including cause and consequences, and resolution.
- Excellent (1%): Comprehensive analysis with critical insights into the incident’s cause, consequences, and aftermath.
- (1%) Technical Accuracy:
- Poor (0.25%): Contains significant inaccuracies or misunderstandings about the incident. Cites at least one reputable source
- Fair (0.5%): Some inaccuracies or minor misunderstandings present.
- Good (0.75%): Mostly accurate with minor errors that do not detract from understanding.
- Excellent (1%): Thorough and precise technical explanation, supported by 5-6 reputable sources.
- (0.5%) Clarity and Organization:
- Poor (0.125%): The abstract is poorly organized and difficult to follow.
- Fair (0.25%): The abstract has some organizational issues but is generally understandable.
- Good (0.375%): The abstract is well-organized and mostly clear, with minor issues in flow. Extended abstract does not exceed 2 pages.
- Excellent (0.5%): Professionally formatted, visually engaging, and aligned with IEEE standards. Report does not exceed two pages.
- (1%) Content Coverage:
Summary Side (2.5%)
- Criterion:
- (1%) Content Coverage:
- Poor (0.25%): The slide fails to capture the key points of the incident, with significant omissions.
- Fair (0.5%): The slide captures some key points but lacks depth and clarity in summarizing the incident.
- Good (0.75%): The slide effectively summarizes the key points of the incident, including cause and consequences.
- Excellent (1%): The slide provides a concise and insightful summary, highlighting critical aspects of the incident with clarity.
- (1.5%) Visual Design:
- Poor (0.375%): The slide is cluttered, with poor use of visuals and text, making it difficult to understand.
- Fair (0.75%): The slide has some visual elements but lacks coherence and effective use of space, leading to a somewhat cluttered appearance.
- Good (1.125%): The slide is visually appealing with a good balance of text and visuals, though there may be minor issues with layout or design.
- Excellent (1.5%): The slide is professionally designed, with clear visuals and a well-organized layout that enhances understanding of the incident. The slide is enjoyable to look at.
- (1%) Content Coverage:
Example Slides:
Cap’n Crunch Incident:
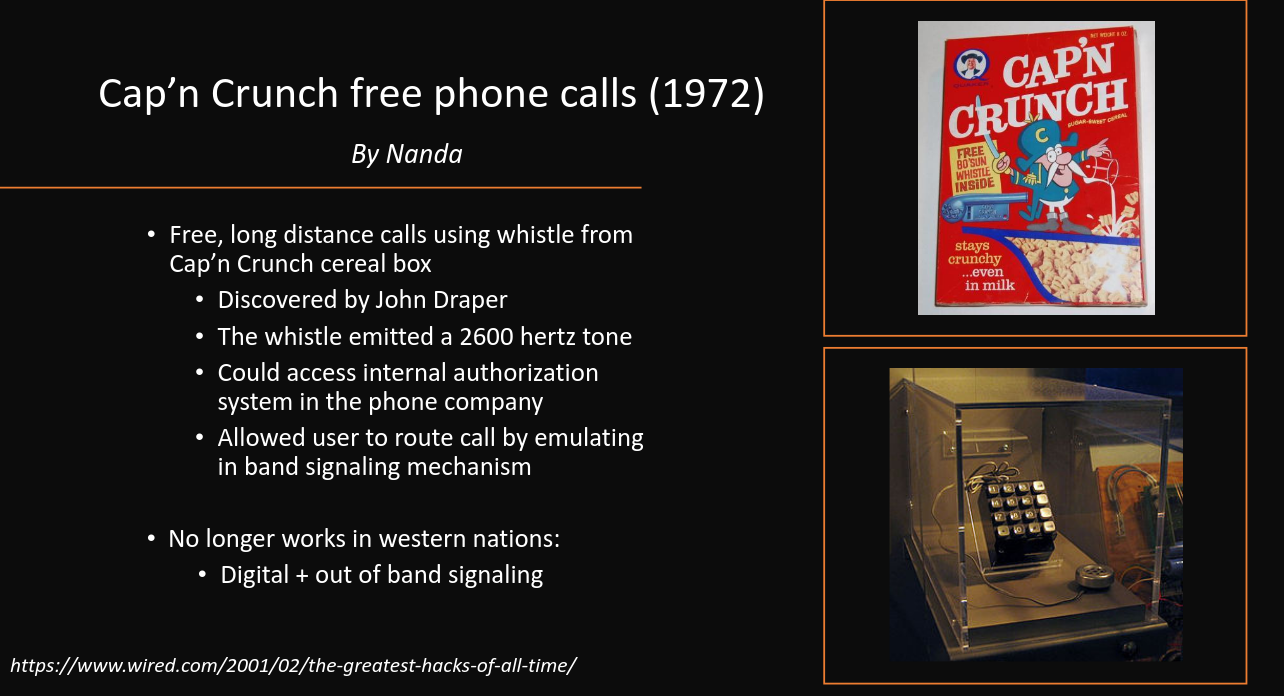
Example Summary Slide for the Cap’n Crunch Incident
This slide was awarded 0.75/1 for content (does not cover enough of the consequences of the incident), and 1.5/1.5 for visual design (the slide is visually appealing and well-organized).
PS2 Modchip Incident:

Example Summary Slide for the PS2 modchip incident.
This slide was awarded 1/1 for content (the slide captures the key points of the incident, including cause and consequences), and 0.75/1.5 for visual design (the slide has some visual elements but lacks coherence and effective use of space, leading to a somewhat cluttered appearance).